Another vulnerability in the Bitcoin Lightning Network
2 min read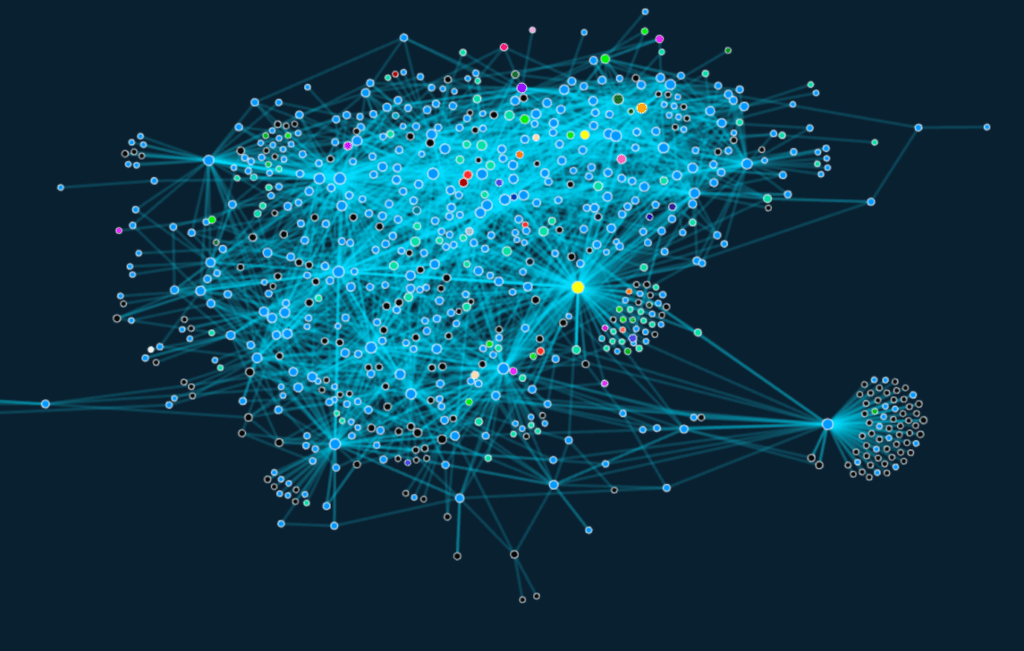
The Lightning Network was designed to improve Bitcoin’s scalability. The project introduced an additional layer of bitcoin blockchain and is intended to increase transaction speed, as it may no longer be approved by all nodes in the network. However, a security audit in September last year identified several security vulnerabilities.
Technology company Blockstream has been involved in the development of the Lightning Network and later developed “c-lightning”, the implementation of the network in C programming language. Blockstream researcher Christian Decker is co-author of an important article. This article primarily addressed the question of whether these mechanisms can be used to gain access to sensitive information.
Two types of potential attacks – probing and timing
A probing attack has been described as an attempt where an attacker, through active probing, attempts to determine the maximum amount that can be transmitted over the target channel. A timing attack was defined as an attempt by a hacker to determine how close a payment target is actually.
Research work has shown that it is actually possible to track payments on any node reachable from the attacker’s node if it has one of the two lower balances on the route. On the other hand, these hazards could be eliminated by private nodes, such as mobile wallets or nodes with a limited operating time, such as personal computers.
Hopefully with the further development of the Lightning project, the above problems will be resolved. Then nothing should stand in the way of mass adoption of bitcoin blockchain.
Summary
Blockchain innovations can be beneficial, but sometimes dangerous. The BTC Lightning Network project described above offers acceleration of transactions, but … This is because the user may face the threat of probing and timing attacks. In general, the potential pluses and minuses of new projects and initiatives (such as this) and their potential consequences for users need to be considered.





![Decentraland: Review & Beginner's Guide [current_date format=Y] 20 Decentraland: Review & Beginner's Guide](https://cryptheory.org/wp-content/uploads/2020/11/decentraland-02-gID_7-300x150.jpg)