Ryuk Bitcoin Ransomware Runs Like Organized Crime
3 min readA style of ransomware known as Ryuk has been particularly successful in the past few years. The ransomware’s backers work in an organized fashion, like a business with developers and recruiters. How does this digital mafia work, and what is the connection to Bitcoin?
Not surprisingly, the Ryuk ransomware requires payment in bitcoin. Naturally, as all transactions are public, this attracts the attention of the police.
To get law enforcement off their tail, Ryuk needs to launder money into fiat. This step in a hacker’s business plan is particularly attractive to law enforcement.
Dirty Bitcoin Laundry
Naturally, some coins that provide more privacy, such as Monero, are even better at concealing identities. However, it seems Ryuk still prefers Bitcoin as it is the most widely adopted cryptocurrency. Thus, it’s easier to get paid.
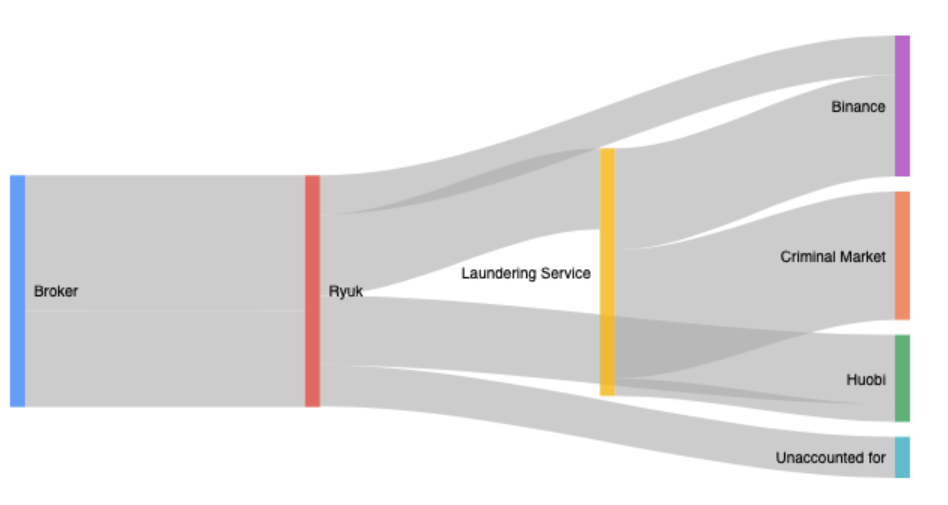
Researchers at HYAS and Advanced Intelligence attempted to track Bitcoin addresses attributed to the Ryuk family of ransomware. Interestingly, these criminals tend to cash out via large exchanges such as Huobi and Binance.
They are large, well-established exchanges that tend to comply with authorities. Both were also founded by Chinese teams who moved their businesses abroad.
HYAS says these exchanges are structured in a way that would not oblige them to hand over any and all information regarding certain accounts.
For example, though both Exchanges require KYC identification, how much these documents are scrutinized is unknown. Until a legal entity asks for additional information, there is no reason to hand over user data.
But not all white-washing of cash happens on big exchanges. Researchers have discovered a number of small wallet addresses popular with Ryuk.
They believe that these wallets are part of organizations that explicitly launder crypto into fiat. They may also exchange bitcoin for other goods or as payment for criminal actions.
Communication
Ryuk’s payments appear to come from a known broker that securely pays ransoms for ransomware victims. It’s estimated that Ryuk is worth more than $150 million.
The criminal organization also works via two ProtonMail e-mail addresses. ProtonMail is an e-mail service fueled by privacy and security. Ryuk does not use chat clients as some ransomware operators do, and its movements indicate thought-out intent.
While other ransomware-wielding criminals will negotiate, Ryuk never has and will only reply with a one-word answer to negotiation requests. Indeed, this signals that Ryuk is part of a professional crime organization.
How to Stop Ransomware
While most companies have up-to-date antivirus software, the real problems remain in other areas. Ryuk uses software to identify highly-desirable targets who are likely to pay.
What companies need to do, HYAS says, is keep themselves from being a target in the first place.
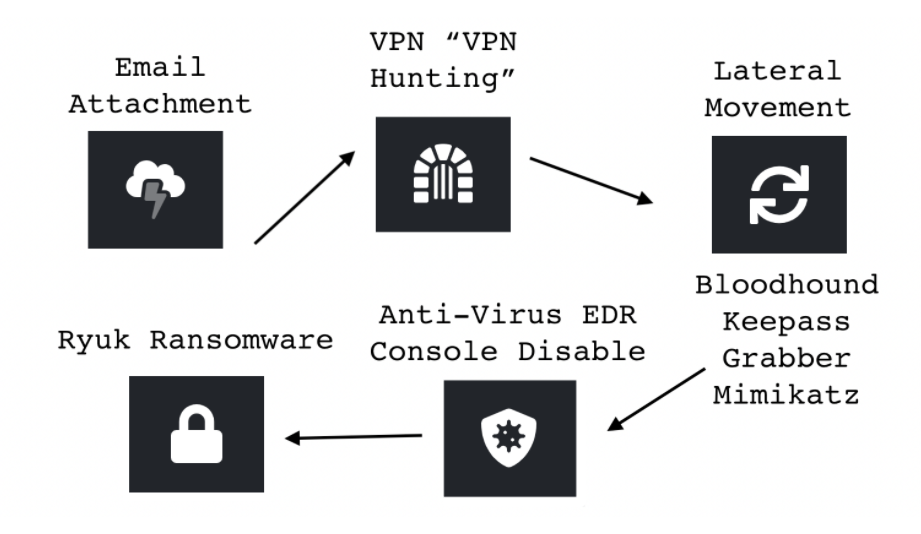
This means not looking like a good mark and stopping precursor malware from making its way to systems in the first place.
To do so, companies need to prevent employees from using Microsoft Office macros, make sure everyone uses two-factor authentication (2FA) and uses secure remote-access tools like Citrix.
Though the number of Bitcoin addresses related to criminal activity tends to be low, criminal associations are a notable roadblock to full crypto adoption.
On a positive note, laundering bitcoin to fiat is no easy task, especially if exchanges cooperate with authorities. With widening appeal to legit companies, Bitcoin is likely to shed its dark reputation.
The post Ryuk Bitcoin Ransomware Runs Like Organized Crime appeared first on BeInCrypto.




![Decentraland: Review & Beginner's Guide [current_date format=Y] 22 Decentraland: Review & Beginner's Guide](https://cryptheory.org/wp-content/uploads/2020/11/decentraland-02-gID_7-300x150.jpg)